Hi to all, my first post made here for helping someone get troubles with IPsec VPN RUT series configuration, after many hours of trial & errors I finally landed on "stable" configuration work like a charm, packets flow between tunnel with no problem on my brand new RUT240 and pfSense APU2 installed on my HQ.
My pfSense hosting many others IPsec instance in parallel, for managing my remote network site stuffs, mainly IP DVR and NVR remote installation.
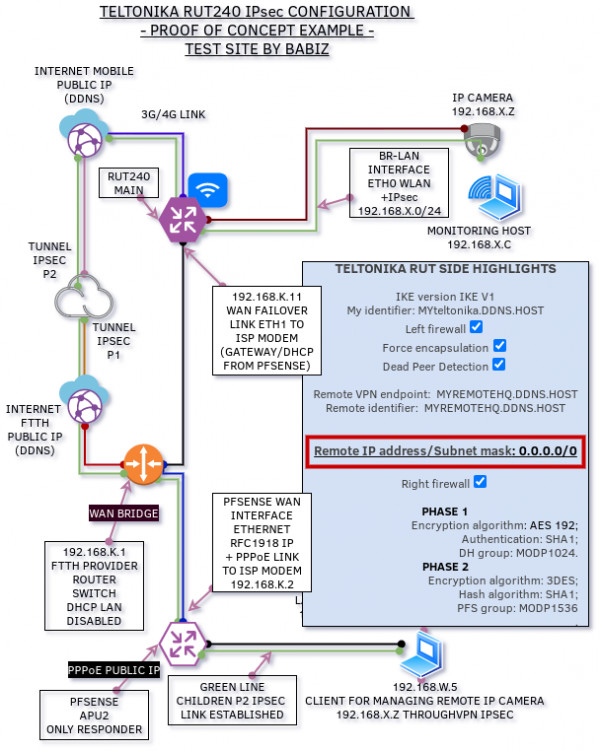
So well, I make this shiny schematic proof of concept, acutally run in my test site, will explain very easy itself. :D
 Ok
Ok
Ok for me, I think setting the remote network subnet/mask to 0.0.0.0/0 do the trick.
Configuration of pfSense side is almost "standard as usual", but I set "Only Responder" flag.
if you want learn more, starting read about strongswan and openwrt, because Teltonika RUT OS is based on OpenWRT / LuCi project, I'm familiar to this things, my reference page when investigating about IPsec om RUT240 not "routing" same as regular other firewall/router appliance, is here:
https://wiki.strongswan.org/projects/strongswan/wiki/UsableExamples
https://forum.archive.openwrt.org/viewtopic.php?id=68509
and some thread on this forum as well https://community.teltonika-networks.com/17128/reach-rut950-ipsec-server-rut950-remote-client-established
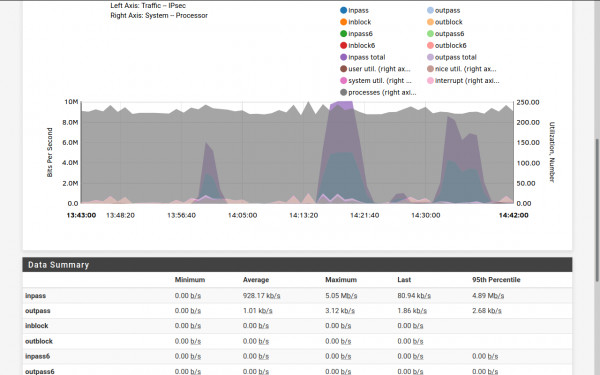
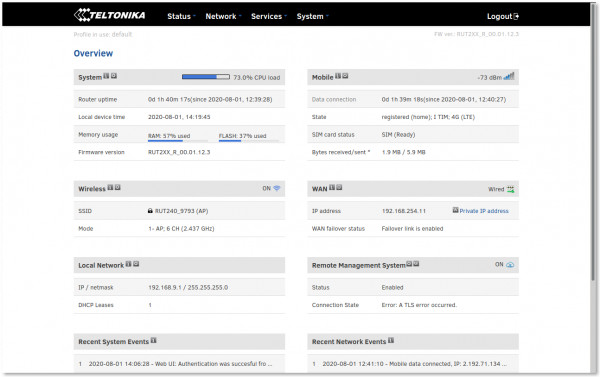
Final notice WARNING: RUT240 hardware based on SoC: Atheros AR9330 rev 1 not much powerful to handle IPsec and high crypto , you can get slow overall performance with some kind of configuration like active Teltonika RMS (another Openvpn hardcoded service eating CPU cycles) and this example is for testing only the "powerful" of troughtput.
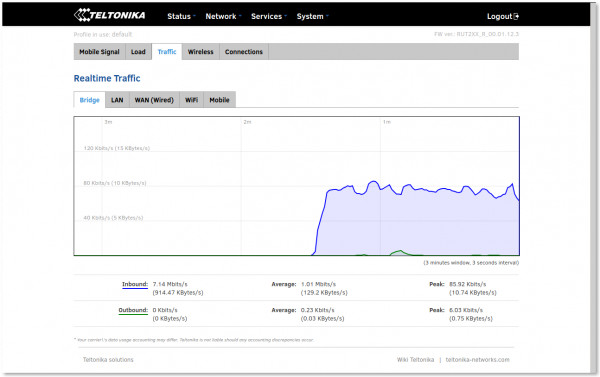
In this scenario I reach to around 5 Mbps stable flow for 80% CPU load meow 
pfSense system load vs. IPsec inbound traffic is irrilevant