Hi,
Sorry for the late response. The answer is yes, it's possible to connect two RUT devices with identical subnets over IPsec VPN.
Let's say your current topology uses 192.168.1.0/24 subnets on both RUT950s.
Now you'll need to choose 2 virtual subnets which will be used for communication between these RUT950s e.g.:
1st RUT950 - 192.168.3.0/24
2nd RUT950 - 192.168.4.0/24
Navigate to Network -> VPN -> IPsec and for 1st RUT950 you'll need to configure local IP address / subnet mask as 192.168.3.0/24 and remote IP address / subnet mask as 192.168.4.0/24. 2nd RUT950 will have inverted configuration - local IP/netmask 192.168.4.0/24 and remote IP/netmask 192.168.3.0/24
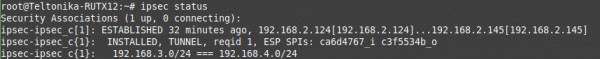
If other settings in your IPsec config are correct then by running command ipsec status in CLI you should see that tunnel is installed between 192.168.3.0/24 === 192.168.4.0/24
Now it'll be needed to do 1:1 NAT by using iptables NETMAP target. These IPtables rules will change source IP for outgoing packets and destination IP for incoming packets.
Navigate to WebUI -> Network -> Firewall -> Custom rules and insert following IPtables rules:
For 1st RUT950:
- iptables -t nat -I POSTROUTING -s 192.168.1.0/24 -d 192.168.4.0/24 -j NETMAP --to 192.168.3.0/24
- iptables -t nat -I PREROUTING -s 192.168.4.0/24 -j NETMAP --to 192.168.1.0/24
For 2nd RUT950:
- iptables -t nat -I POSTROUTING -s 192.168.1.0/24 -d 192.168.3.0/24 -j NETMAP --to 192.168.4.0/24
- iptables -t nat -I PREROUTING -s 192.168.3.0/24 -j NETMAP --to 192.168.1.0/24
Now all that's left is to test configuration, from LAN client of 1st RUT950 ping any remote LAN device by using 192.168.4.0/24 addressing and for LAN2 to LAN1 use 192.168.3.0/24 addressing.
By this point LAN to LAN communication is established but RUT950s cannot ping each other. For RUT950 to be able to ping each other it's needed to add additional routing rules:
On 1st RUT950 use command: ip route add 192.168.4.0/24 dev eth1 src 192.168.1.1 table 220
On 2nd RUT950: ip route add 192.168.3.0/24 dev eth1 src 192.168.1.1 table 220
Note: when adding route, after dev you should specify interface name which is used to establish IPsec tunnel, this example uses eth1 - wired wan.