Hi, thank you for your response. I reset all install the last firmware an start from scratch as you suggest and now I'm able to connect to cam using public IP. Good
Now the second step...I need to do the same but within a VPN (to Azure).
What I did is create the vpn gtw on Azure and configure point-to-site connections, then I download the OpenVpn client configuration file. On the router using the web ui I create the OpenVPN client configuration, flag to use a file, upload it and save. Good, it works; al also can "ping" from router utilities a linux box in Azure vnet.
Azure vnet is 10.60.0.0/16 with two subnet: 10.60.0.0/24 for the gtw and 10.60.10.0/24 for "servers" (here is my linux box). P2S network is 10.61.0.0/16.
On the router I add another port forward rule like the one that you suggest me BUT using openvpn as the source zone and of course with another external port (8081).
This solution, does not work. from linux box on Azure (that is 10.60.10.4) I cannot connect to cam through router vpn ip (that is 10.61.0.2).
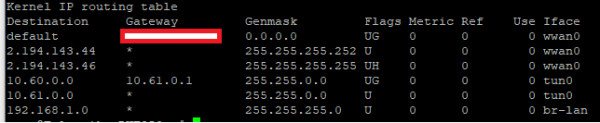
this is the route table in router:
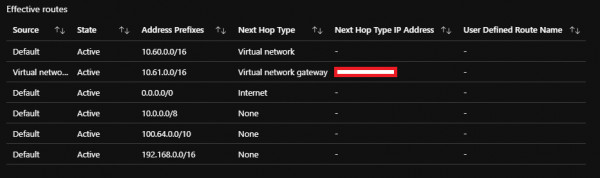
and this is the route table of linux box in azure:
Any suggestion?
Thank you