Me again,
we need support for that RUTX11. Is it possible to get an professional support for that devices with SLAs, Tickets and so on?
For that problem with the vpn connection between the RUTX11 and our Fortigate:
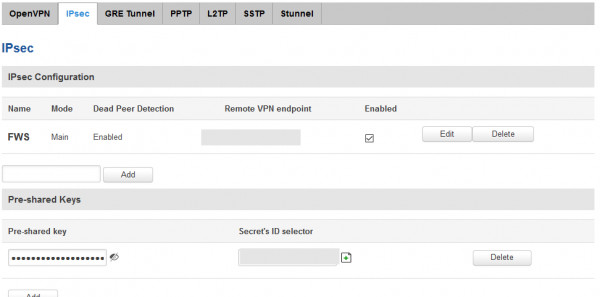
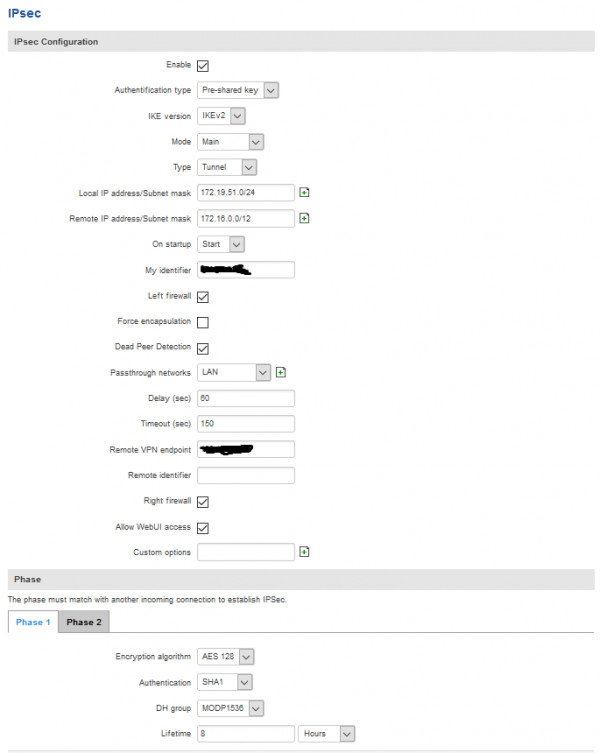
Here is a working configuration from one RUT240:
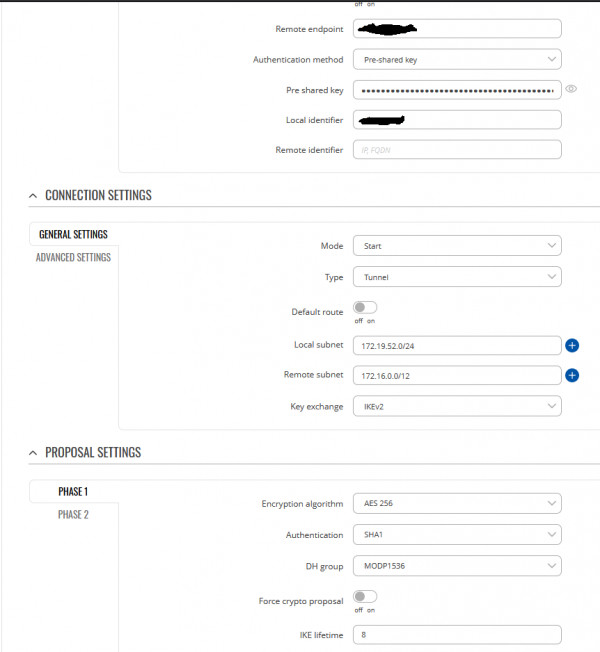
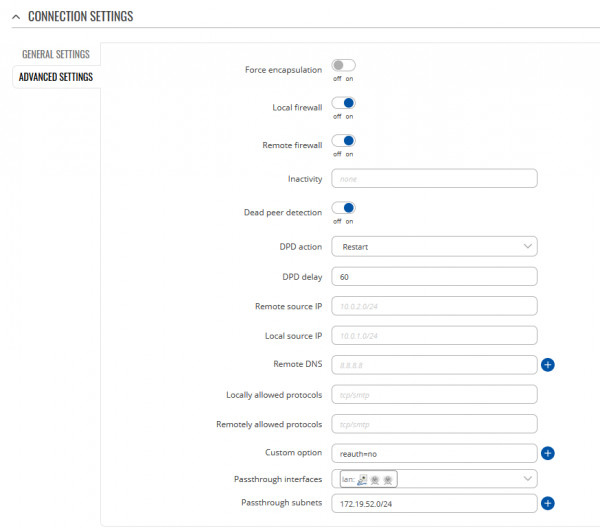
And here the configuration from the RUTX11 which is not working:
Note:
The RUT240 uses AES128, because AES256 is so much slower on that little router. The RUT240 is also working with AES256, we selectes AES128 only because of performance issues.
We would like to replace 30 of our Lancom routers with a different product, but without vpn the RUTX11 its useless.