Hello Martin.
I still can't get (ping) to address 172.30.51.1.
This is route on server side
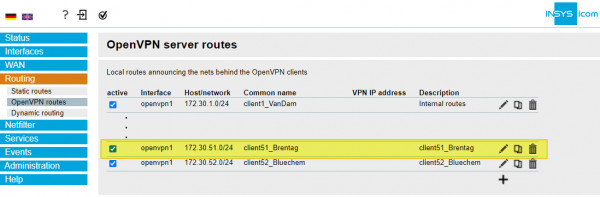
There are some details from Open VPN
serverUpdated,Tue Apr 26 08:52:35 2022
Common Name,Real Address,Bytes Received,Bytes Sent,Connected Since
client51_Brentag,37.188.242.185:53524,1299867,1258928,Tue Apr 26 08:00:31 2022
ntb_bara,185.71.233.32:1194,7311514,9995955,Tue Apr 26 07:41:32 2022
ROUTING TABLE
Virtual Address,Common Name,Real Address,Last Ref
10.1.0.26,ntb_bara,185.71.233.32:1194,Tue Apr 26 08:52:35 2022
fd19:433a:30e5:1c2c::1005,ntb_bara,185.71.233.32:1194,Tue Apr 26 07:41:33 2022
172.30.51.0/24,client51_Brentag,37.188.242.185:53524,Tue Apr 26 08:00:32 2022
10.1.0.10,client51_Brentag,37.188.242.185:53524,Tue Apr 26 08:52:34 2022
fd19:433a:30e5:1c2c::1001,client51_Brentag,37.188.242.185:53524,Tue Apr 26 08:00:32 2022
GLOBAL STATS
Max bcast/mcast queue length,1
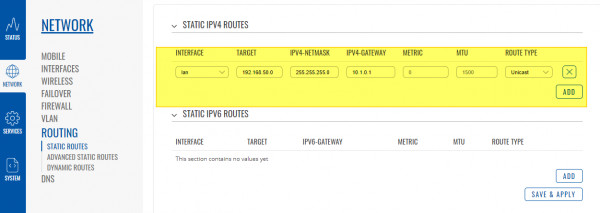
new static route
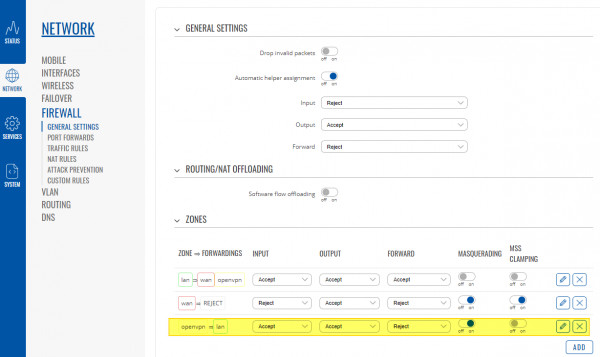
I allowed this zone
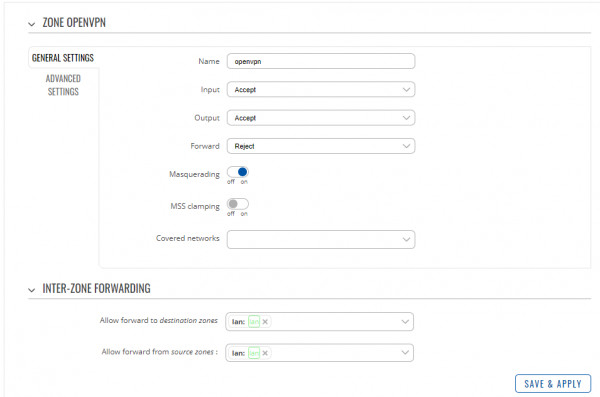
zone settings
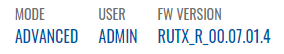
Mode and fw version
Ping is without changing
C:\>ping 172.30.51.1
Pinging 172.30.51.1 with 32 bytes of data:
Reply from 10.1.0.10: Destination port unreachable.
Reply from 10.1.0.10: Destination port unreachable.
Reply from 10.1.0.10: Destination port unreachable.
Reply from 10.1.0.10: Destination port unreachable.
Ping statistics for 172.30.51.1:
Packets: Sent = 4, Received = 4, Lost = 0 (0% loss),
Do you have some idea?