Hello,
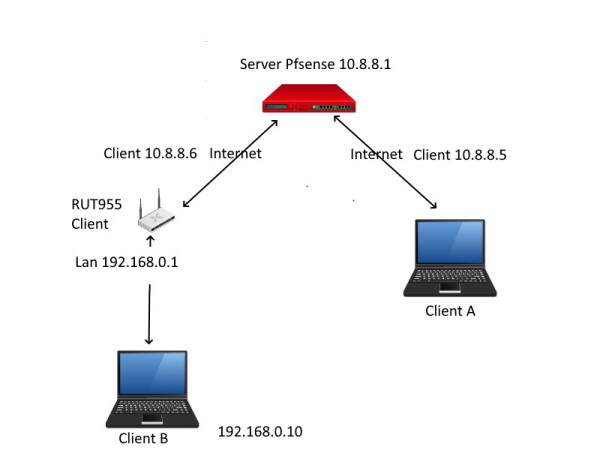
I went back to a wireguard configuration with a PFsense as a server.
I manage to ping client A address in 10.8.8.1 / 10.8.8.6
But I would still like to be able to communicate from my Client A to Client B and I can't ping.
I access the RUT955 web in 10.8.8.6 but not in 192.168.0.1.
Configuration Wg server Pfsense:
IP 10.8.8.1/24
Pfsense Client A Wg Configuration:
AllowIp: 10.8.8.5/32
192.168.0.0/24
Pfsense Client B Wg Setup:
AllowIp: 10.8.8.6/32
192.168.0.0/24
Configuration Wg client A Windows:
[Interface]
Address = 10.8.8.5/32
MTU = 1360
[Peer]
AllowedIPs = 0.0.0.0/1, 128.0.0.0/1 (I also tried 0.0.0.0/0)
PersistentKeepalive = 25
Configuration Wg client B RUT955:
[Interface]
Address = 10.8.8.6/32
MTU = 1360
[Peer]
AllowedIPs = 0.0.0.0/0 (If I put 0.0.0.0/1 , 128.0.0.0/1 the RUT955 is no longer available)
Route Allowed IPs = Ok
PersistentKeepalive = 25
Thanks