Hello,
The workflow in your case would be to first create a separate firewall zone for your VLAN on port 2, if you have not already, and then create a traffic rule preventing device access on HTTP, HTTPS, SSH ports.
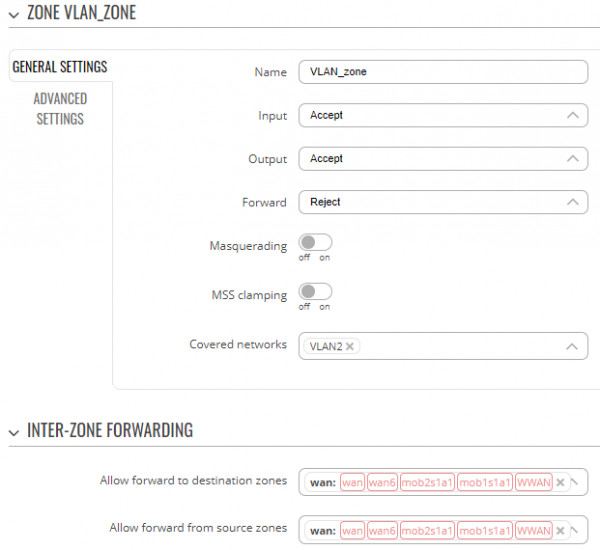
In the WebUI navigate to Network -> Firewall -> General settings. Add a new firewall zone, attach VLAN interface to Covered networks option and allow forwarding to WAN.
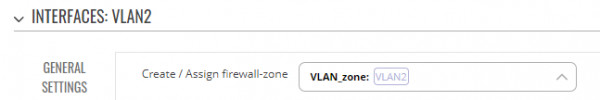
Make sure your VLAN interface is attached to this firewall zone in Network -> Interfaces by editing VLAN interface settings and switching to Firewall settings tab.
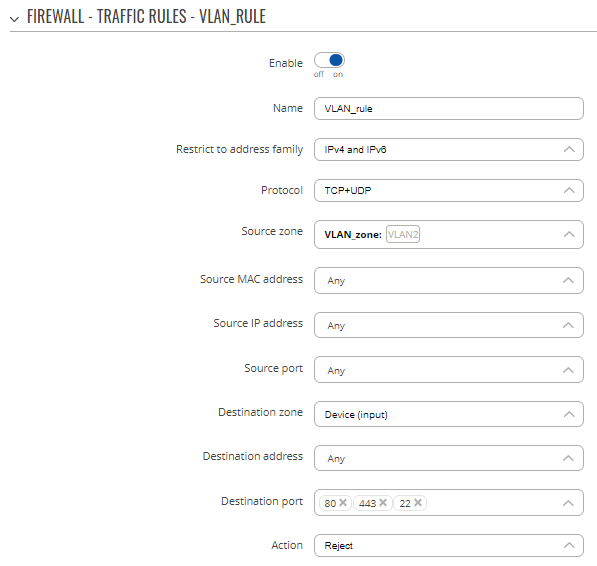
Create a new traffic rule rejecting connections to the device, originating from VLAN firewall zone in Network -> Firewall -> Traffic rules. Scroll to the bottom of the page, add a new instance of Open ports on router type. Configure the following:
- Source zone: <Your_VLAN_firewall_zone>
- Destination zone: Device (input)
- Destination port: 80, 443, 22 (unless you have replaced default values in System -> Administration -> Access control)
- Action: Reject
This should prevent device access on VLAN associated with port 2.
Best regards,