Hello,
To associate 2 subnets with a single TLS client, you will need to make some changes via SSH.
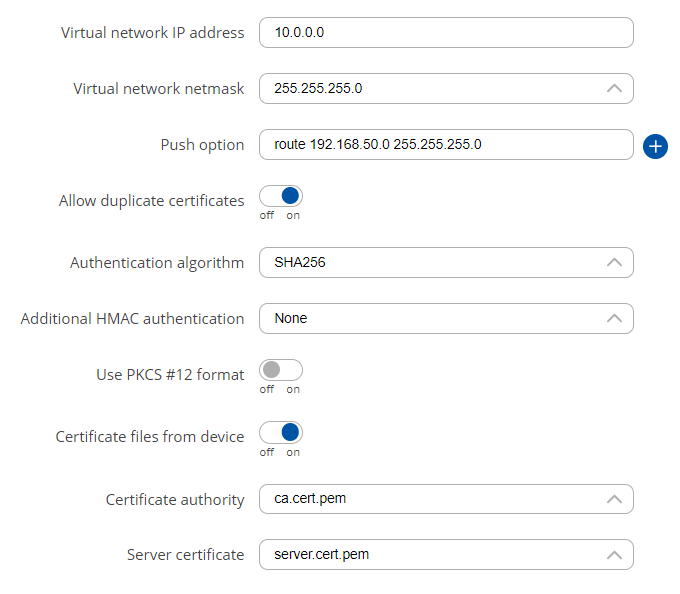
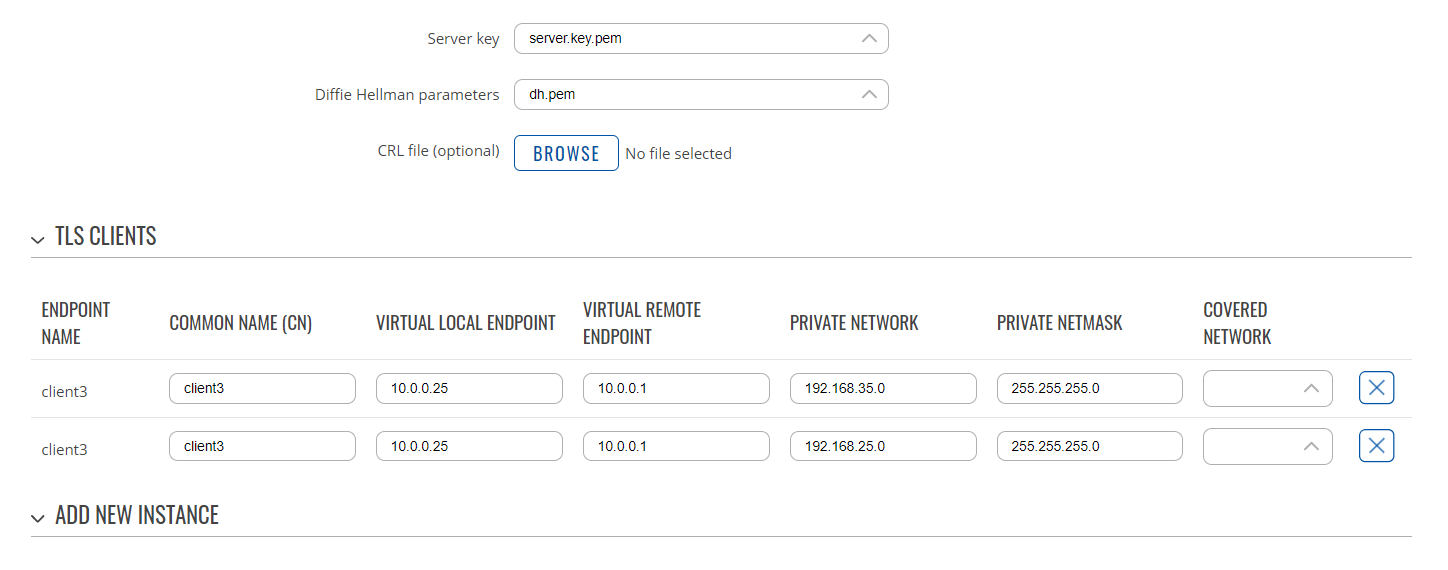
First, configure OpenVPN server and its TLS clients via WebUI. I will put some images for reference.
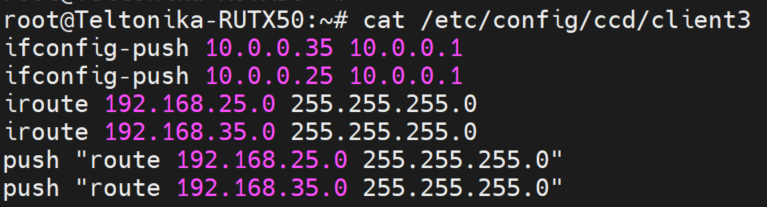
Next, you will need to create a 'client' file on the server where you will put the associated routes with the client (I will use 'client3' throughout this configuration). You will need to create and edit the file in '/etc/config' folder.
Connect to the device via SSH and execute the following commands:
- mkdir /etc/config/ccd
- touch /etc/config/ccd/client3
- vi /etc/config/ccd/client3
You will enter the text editor. Press 'i' to start editing. You can navigate with arrow keys. Paste the following lines, but change the IP networks (192.168.25.0/24 and 192.168.35.0/24) to your own (192.168.31.0/24 and 192.168.32.0/24). Also, change the tunnel IP addresses (10.0.0.x) to the ones you use:
ifconfig-push 10.0.0.35 10.0.0.1
ifconfig-push 10.0.0.25 10.0.0.1
iroute 192.168.25.0 255.255.255.0
iroute 192.168.35.0 255.255.255.0
push "route 192.168.25.0 255.255.255.0"
push "route 192.168.35.0 255.255.255.0"
To save and exit the editor, press 'esc' button, then type ':wq' and press enter.
Next, you will have to edit OpenVPN configuration file:
You will enter the text editor again. Find the following line:
- option client_config_dir '/etc/openvpn/ccd'
Replace this line (directory path) with:
- option client_config_dir '/etc/config/ccd'
Save the changes and exit editor.
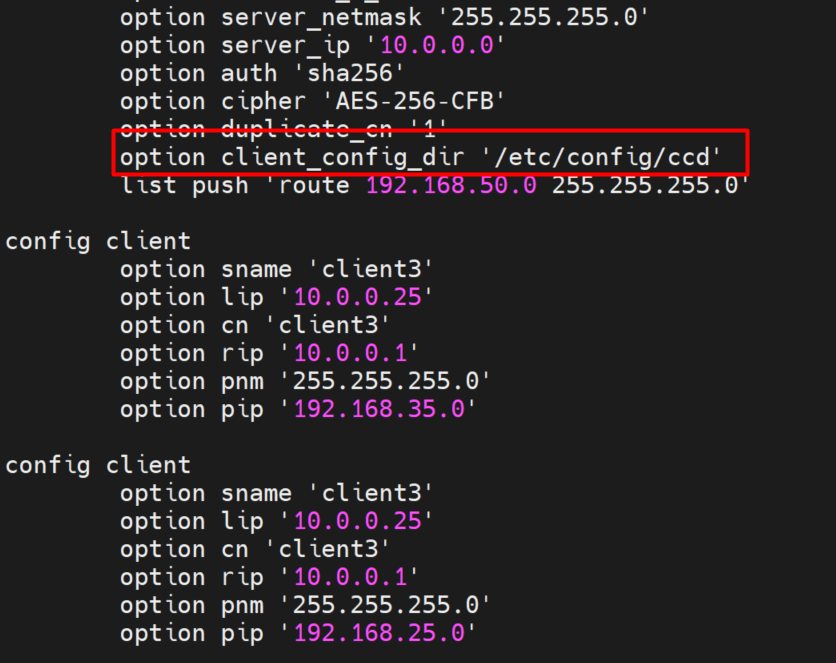
Restart OpenVPN service via the following command:
- /etc/init.d/openvpn restart
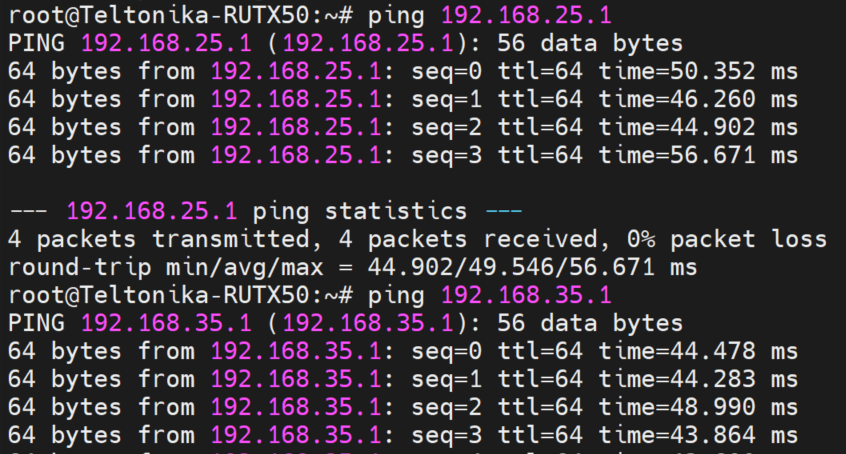
Everything should work now.
Kind Regards,
Andzej