Hello,
I apologize for any misunderstanding, as I am new to OpenVPN and have primarily worked with WireGuard before. However, WireGuard does not seem meet my requirements in this case.
I would like to connect three RUTX11 routers via VPN, where all routers and clients operate on the same network. I prefer not to create separate subnets for each router. Here is my planned setup:
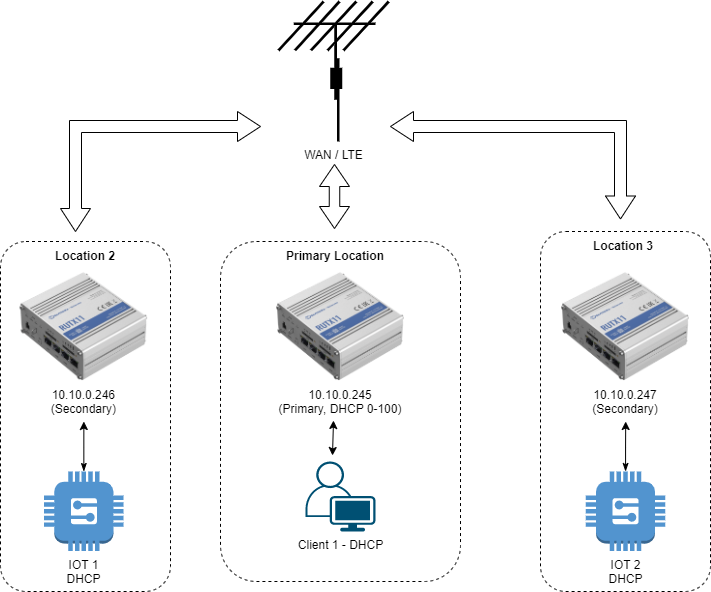
The objective is to create a mobile network deployment solution. We already have a network with all the clients, dhcp and devices configured on the primary router. We want to take two routers and some of the clients and deploy them in different locations (Using LTE), allowing them to reconnect through the site-to-site VPN. The secondary routers woul'd only be turned on for such mobile deployments, and are not a usual part of the network.
I followed this Wiki-guide to set up the primary RUTX11 as the server and the other two as clients:
Connecting two same subnet office networks using OpenVPN bridge (TAP) on RUTX
The Open-VPN Server on the primary RUTX11 is reachable via a public ip thats constantly updated via dyndns.
Now, here's the issue:
The connection works, but only one device stays connected. After approximately 2 minutes (which matches the keepalive 10 120 value in the configuration), secondary 1 (246) disconnects, and secondary 2 (247) connects. This switching continues indefinitely in a loop.
Do I need to adjust any configurations to enable this scenario? Or should I approach it in a completely different way?
I attached the troubleshoot file for all three devices. Allthough i only see the disconnect by pinging the router IP-s from clients. In the UI it does not show. If i tail the openvpn logread output, all i see is the timeout and connection restart.
Thank you for your input :) and i hope my issue is understandable